In recent times, the usage of edge computing has gained immense reputation throughout varied sectors, together with the protection trade.
With the evolution of house expertise, edge computing has been expanded to space-based edge computing, offering extra advantages for high-tech protection operations. Area-based edge computing can allow sooner knowledge processing, improved communication capabilities, and enhanced safety measures that will complement protection models to attain the options of contemporary warfare.
Nonetheless, space-based edge computing comes with its personal set of challenges that have to be addressed to completely exploit its potential. This text will look at how space-based edge computing might be leveraged for protection purposes, the challenges concerned, and methods to overcome these to make the most of the expertise to its full potential.
What’s space-based edge computing?
Area-based edge computing is a distributed computing paradigm that entails processing and analyzing knowledge at or close to the supply of information technology in house. It combines the idea of edge computing, which entails processing knowledge regionally on the fringe of a community, with space-based techniques equivalent to satellites and different spacecraft.
It’s designed to scale back the latency and bandwidth necessities of information transmission by processing knowledge as near its supply as potential. That is particularly vital for purposes that require real-time processing and decision-making, equivalent to these within the fields of earth statement, local weather monitoring, and catastrophe administration.
Area-based edge computing techniques usually contain a community of interconnected space-based and ground-based nodes that work collectively to course of and analyze knowledge. These nodes could embrace satellites, drones, floor stations, and different units that accumulate and transmit knowledge to the sting of the community.
By leveraging the facility of distributed computing, space-based edge computing allows organizations to course of and analyze large quantities of information in actual time, making it potential to shortly determine patterns, anomalies, and tendencies that may in any other case go unnoticed.
This might help organizations to make extra knowledgeable choices and reply extra shortly to altering circumstances, equivalent to in protection operations.
Leveraging Area-Primarily based Edge Computing in Protection Purposes
Area-based Edge computing has turn out to be significantly essential within the protection sector, the place split-second synchronization and decision-making can imply the distinction between victory and defeat.
The arrival of space-based edge computing has opened up new alternatives for the protection trade, offering dependable and safe entry to important info in distant and difficult environments. That is the principle demand-driving issue out there, resulting in substantial development.
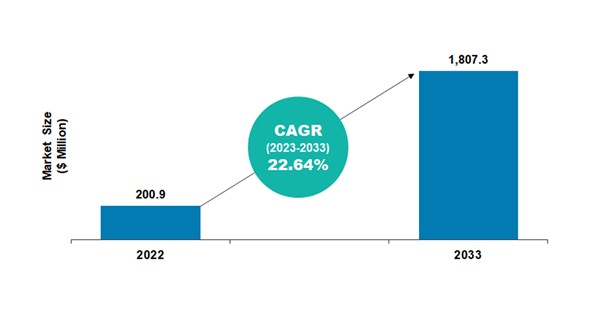
In line with knowledge insights from BIS Analysis, the worldwide space-based edge computing market is estimated to succeed in $1,807.3 million in 2033 from $200.9 million in 2022, at a CAGR of twenty-two.64% throughout the forecast interval 2023-2033.
Click on right here to obtain a free pattern
The projected development is owing to the demand within the protection sector as space-based edge computing has the next purposes:
• One instance of the potential of space-based edge computing in protection is the usage of unmanned aerial techniques (UASs) for intelligence, surveillance, and reconnaissance (ISR) missions. These UASs can accumulate knowledge utilizing sensors equivalent to cameras, infrared (IR), and electro-optical (EO) techniques.
By processing all the info on platforms and speaking with one another in a “mesh community,” these UASs could make autonomous choices as a distributed cluster of belongings. This method maximizes bandwidth and reduces the danger of system overload.
• In land-based operations, by bringing analytical knowledge storage and networking assets nearer to the place knowledge is being collected, edge computing reduces bandwidth utilization and accelerates response occasions.
This expertise has turn out to be much more important with the introduction of 5G expertise and developments in knowledge processing occasions. In distant areas with restricted web entry, troopers can now entry confidential info equivalent to climate knowledge, pc efficiency knowledge, and different knowledge to make knowledgeable choices.
• In airborne operations, space-based edge computing offers an infinite benefit in situational consciousness and fast decision-making. The U.S. Air Pressure (USAF) has applied a variety of automated sources that give pilots entry to info past what’s supplied to them.
For instance, throughout a technological train for the Air Pressure’s Superior Battle Administration System (ABMS), Amazon Internet Companies (AWS) demonstrated the flexibility to implement a tactical edge node answer utilizing extremely sturdy community entry and communications. This answer included abilities equivalent to DevSecOps, implementation of synthetic intelligence (AI) and machine studying (ML) purposes, Kubernetes Cluster on the edge, and the capability to switch growth code from unclassified to categorized networks.
• In naval operations, space-based edge computing can play a vital position in sending and receiving info with decreased delay and extra sorted info to the ships. The U.S. Navy is making ready to make important investments in cloud computing infrastructure put in on ships as a part of its long-term plan for network-centric naval fight.
Tactical edge computing infrastructure might be put in on plane carriers, amphibious ships, and different vessels, enabling the U.S. Navy to function data-rich purposes removed from U.S. territory and with out the assistance of a centralized community.
Furthermore, established analysis companies such because the Protection Superior Analysis Initiatives Company (DARPA) have undertaken tasks using space-based edge computing.
For example, the Blackjack program has been beneath DARPA since 2017 to develop a world, high-speed community in low Earth orbit (LEO) that’s extra linked, resilient, and chronic than already out there Nationwide Safety Area (NSS) belongings. The launch of Blackjack is scheduled to start in 2024.
The aim is to attain LEO efficiency similar to that of present geosynchronous techniques however with a decrease price of $6 million per orbital node whereas assembly the dimensions, weight, and energy constraints of the business bus.
In line with the DARPA company, Blackjack will incorporate edge computing that may allow the constellation to shortly analyze knowledge and enhance the situational consciousness of the army, resulting in sooner decision-making.
Furthermore, the DARPA company goals to reveal autonomous orbital operations, which embrace on-orbit distributed resolution processors, to enhance satellite tv for pc administration.
The Cybersecurity Problem
The potential threat of cyberattacks on space-based edge computing units can compromise the integrity and safety of delicate knowledge, resulting in catastrophic penalties.
Area-based edge computing faces quite a few cybersecurity challenges that require efficient options to mitigate the dangers. These challenges might be broadly categorized into the next:
1. Knowledge Storage, Backup, and Safety Dangers: The shortage of bodily safety safeguards in edge computing environments presents a big threat for knowledge saved on the edge. Attackers may simply copy knowledge from reminiscence sticks or take away disks from edge computing assets, doubtlessly stealing complete databases. Moreover, constrained native storage choices at edge computing amenities could make it tough or not possible to again up essential information, leaving no backup copy to revive the database within the occasion of an incident.
2. Perimeter Protection Dangers: Edge computing poses challenges for perimeter protection because it widens the IT perimeter. The credentials for edge techniques are sometimes saved on the edge since these techniques have to authenticate their purposes with companion apps within the knowledge heart. A compromise in edge safety may reveal login info for knowledge heart belongings, drastically extending the extent of the safety incident. Moreover, edge structure variances in internet hosting could restrict safety choices, making it more difficult to cope with perimeter assaults.
3. Dangers Related to Cloud Computing: Completely different cloud options deal with edge elements in varied methods, and the particular connection between the sting and the cloud determines the kind of hazards related to cloud computing. Offering secure entry to cloud apps and assets may be tough, significantly if edge units are easy controllers, as is commonly the case. Subsequently, entry management, edge-to-cloud connection, and different safety measures have to be fastidiously thought-about.
4. Software program Vulnerabilities: Software program vulnerabilities, that are defects within the code that might enable attackers to entry a system, are a possible weak point that have to be addressed. Errors in software program coding or design might be the reason for these vulnerabilities. Software program with vulnerability administration capabilities actively searches the community for vulnerabilities, identifies them, and offers recommendations on methods to repair them, lowering the opportunity of additional safety breaches.
Overcoming the Dangers
1. Machine Discovery: The preliminary step in securing edge computing networks is system discovery. It entails figuring out and documenting each system on the community to make sure that a database of every system and the info it produces is maintained. This info additionally contains figuring out the particular threats every system poses. Utilizing monitoring instruments helps to maintain monitor of all units and ensures immediate intrusion detection.
2. Community Edge Safety: Area-based edge computing requires direct web entry to make use of cloud providers. This will increase the danger of hostile exercise coming from the web and into the corporate community. Nonetheless, efficient community edge safety offers a safer and dependable connection to firm assets by means of the web. Anti-malware, net filtering, next-generation firewalls, and intrusion prevention techniques are a few of the choices out there for community edge safety.
3. Cloud Edge Safety: Edge computing is vulnerable to assaults as a result of knowledge have to be transmitted from the sting to the cloud and vice versa. Sturdy cloud safety prioritizes vital safety components equivalent to encryption for each native knowledge storage and knowledge transmission between edge units and the community core.
Challenge OpenTitan: Google’s Initiative
With a purpose to present safety measures to the trade at giant, Google opened sourced a challenge in 2019 after introducing chip-level safety into its knowledge facilities.
Challenge OpenTitan, which additionally contains options equivalent to self-testing for reminiscence tampering on every processor boot, seeks to generate the utmost quantity of openness and safety on the chip stage.
To create the usual and roll out the expertise by means of 2022 and much past, Google has teamed up with knowledge giants equivalent to Western Digital and Seagate.
U.S. Area Pressure’s Initiative to Clear up Edge Computing Challenges in Area
In 2022, Spacewerx, the innovation arm of the U.S. Area Pressure, partnered with Wallaroo Labs, a New York-based startup, to resolve edge computing challenges in house.
Utilizing Wallaroo’s AI/ML platform, the U.S. Area Pressure (USSF) is simulating AI and machine studying algorithms on edge computer systems in house to handle the problem of the comparative lack of compute capability aboard a spacecraft in comparison with terrestrial capability.
Conclusion
With the expansion of business house ventures and the enlargement of space-based actions past Earth’s orbit, there might be a better want for processing and analyzing huge quantities of information in actual time.
Area-based edge computing can present the mandatory computational energy to make this potential whereas additionally lowering the reliance on Earth-based assets and infrastructure.
The event of latest applied sciences, equivalent to AI and ML, is anticipated to enhance the effectivity and safety of space-based edge computing.
Because of this, the potential purposes of space-based edge computing in protection, scientific analysis, and business actions are anticipated to proceed to broaden, driving innovation and progress within the discipline of house exploration.
to know extra concerning the rising applied sciences in your trade vertical? Get the most recent market research and insights from BIS Analysis. Join with us at good day@bisresearch.com to study and perceive extra.